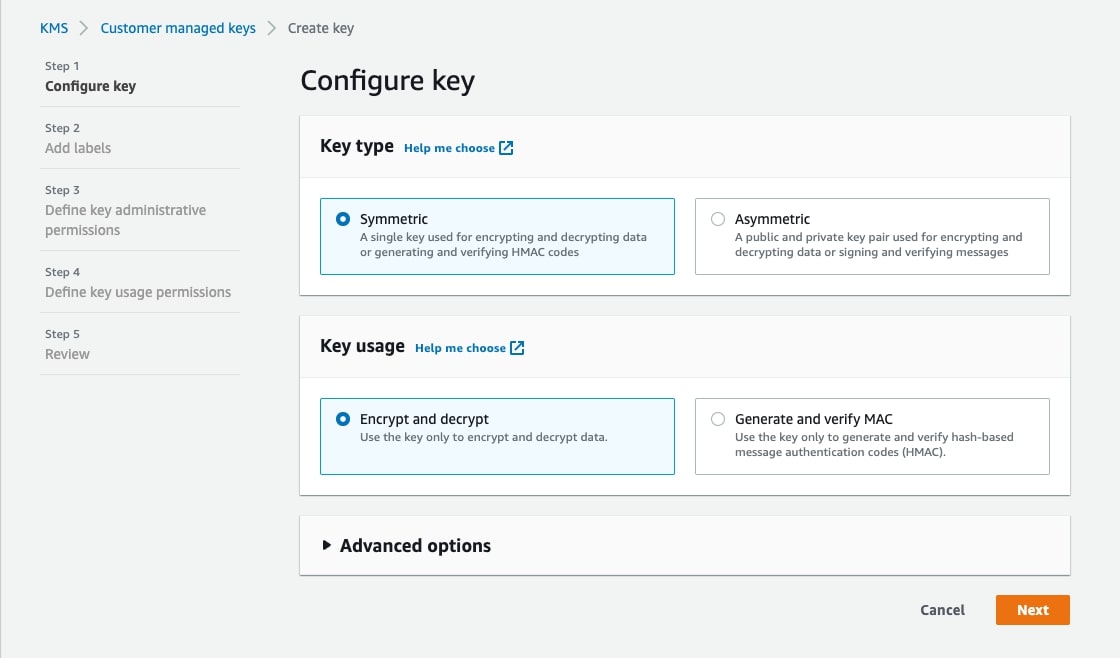
How to Implement BYOK Quickly and Efficiently
Delving into the right way to implement BYOK, this introduction immerses readers in a novel and compelling narrative, with informal language model that’s each partaking and thought-provoking from the very first sentence. BYOK, or Deliver Your Personal Key, has grow to be an important a part of fashionable IT safety, permitting organizations to take care … Read more