Easy methods to bind qbittorrent to vpn is a complete information that delves into the intricacies of digital personal networks (VPNs) and BitTorrent, offering an in depth perception into their interplay with on-line protocols. By understanding the basics of VPNs and BitTorrent, customers can navigate the dangers related to on-line actions, guaranteeing most anonymity.
This information isn’t merely a technical tutorial however an exploration of the important instruments required for safe on-line shopping. It takes under consideration the nuances of VPN companies, the efficiency of BitTorrent shoppers, and the configuration settings essential for seamless integration.
Understanding the Fundamentals of VPN and Bittorrent
Digital personal networks (VPNs) and BitTorrent are two distinct applied sciences that serve completely different functions however usually work together in on-line environments. A VPN is a service that creates a safe, encrypted connection between a person’s machine and a VPN server, permitting customers to browse the web privately and securely. However, BitTorrent is a peer-to-peer (P2P) file-sharing protocol that permits customers to share and obtain giant information from a community of customers.
On this context, BitTorrent functions, equivalent to qBittorrent, facilitate file downloads by dividing information into smaller items and sharing them throughout a community of customers. Nonetheless, with out correct safety measures, BitTorrent customers are uncovered to potential safety dangers, together with:
Frequent BitTorrent Vulnerabilities
BitTorrent functions are sometimes the goal of cyber attackers on account of their widespread use for P2P file sharing. This makes them weak to varied safety dangers, together with:
-
Malware and Ransomware Assaults:
BitTorrent functions can be utilized to distribute malware and ransomware, which might compromise customers’ gadgets and knowledge. -
IP Tackle Leaks:
With no VPN, BitTorrent customers can expose their IP addresses to the general public, making it simpler for cyber attackers to hint and observe their on-line actions. -
Information Breaches:
Unauthorized entry to customers’ knowledge can happen when utilizing unsecured BitTorrent functions or P2P networks, compromising delicate info.
Understanding the safety dangers related to BitTorrent is essential in utilizing the service responsibly. The need of VPNs for on-line privateness and safety will be illustrated as follows:
When utilizing on-line companies like BitTorrent, it is important to make use of safety measures to forestall potential vulnerabilities. A VPN can masks a person’s IP tackle, encrypt web site visitors, and shield in opposition to varied cyber threats. This ensures confidentiality, integrity, and authenticity of the info exchanged.
Kinds of VPNs
There are numerous sorts of VPNs obtainable, together with:
| Sort | Description |
| PPTP (Level-to-Level Tunneling Protocol) | A low-security VPN protocol appropriate for shopping functions. |
| OpenVPN | A high-security VPN protocol ultimate for demanding functions. |
The VPN know-how is designed to make sure the web confidentiality and safety of customers’ knowledge, particularly in circumstances the place customers share information, like in BitTorrent networks.
“Utilizing a VPN can masks your IP tackle, defending your knowledge from unauthorized entry.”
Configuring Bittorrent to Work with VPN
To make sure a seamless expertise whereas utilizing BitTorrent with a VPN, you want to configure each the VPN and BitTorrent shoppers accurately. This step-by-step information will stroll you thru the method, highlighting the important settings and potential points you may encounter.
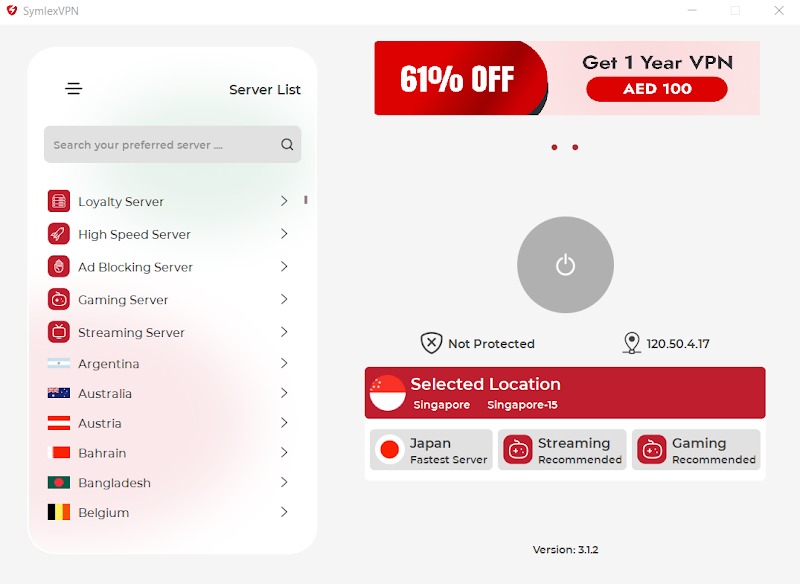
Step 1: Configure VPN Settings
Your VPN shopper’s settings will decide how your web site visitors is routed. Sometimes, you will discover the settings for routing site visitors via the VPN within the superior or preferences part of your VPN shopper. Make sure that the VPN is ready to route all site visitors, not simply particular functions.
- Open your VPN shopper and navigate to the superior or preferences part.
- Search for the choice that lets you route all site visitors or choose a particular possibility for routing BitTorrent site visitors.
- Allow this selection and save the modifications.
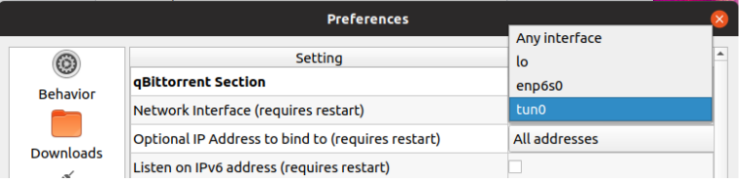
Step 2: Configure BitTorrent Settings
Within the BitTorrent shopper, you will must configure the settings to attach via the VPN. That is normally carried out by choosing the VPN adapter because the outgoing interface for the BitTorrent shopper.
- Open your BitTorrent shopper and navigate to the settings or preferences part.
- Search for the choice that lets you change the outgoing interface.
- Choose the VPN adapter because the outgoing interface and save the modifications.
Step 3: Take a look at the Connection
After configuring each the VPN and BitTorrent shoppers, check the connection to make sure seamless integration.
- Open a brand new window or tab to check the connection.
- Attempt downloading a file or seeding a torrent to confirm that your BitTorrent shopper is working with the VPN.
- Test for any errors or connectivity points, and modify the settings accordingly.
Troubleshooting Frequent Points
Whereas configuring BitTorrent to work with VPN, you may encounter some frequent points, equivalent to connectivity issues or gradual obtain speeds. This is tackle these points.
Subject 1: VPN Not Routing BitTorrent Visitors
In case your BitTorrent shopper isn’t routing site visitors via the VPN, it might be as a result of VPN shopper settings or the BitTorrent shopper settings. Test the VPN shopper settings to make sure that all site visitors is being routed, and modify the BitTorrent shopper settings to pick out the VPN adapter because the outgoing interface.
Subject 2: Gradual Obtain Speeds
Gradual obtain speeds will be attributed to varied elements, together with web throttling, server congestion, or a poor VPN connection.
- Test for any web throttling or site visitors shaping by your ISP.
- Attempt utilizing a special VPN server or protocol to see if it improves obtain speeds.
- Alter the BitTorrent shopper settings, such because the connection technique or add/obtain limits, to optimize obtain speeds.
By following these steps and troubleshooting frequent points, you can configure BitTorrent to work seamlessly together with your VPN, guaranteeing a safe and personal expertise whereas downloading information or seeding torrents.
Monitoring and Sustaining Qbittorrent-VPN Safety
Monitoring the safety of your Qbittorrent and VPN connections is important to forestall potential dangers equivalent to knowledge leaks, cyber assaults, and unauthorized entry. To do that successfully, you want to implement a sturdy safety plan that features monitoring on-line actions, figuring out potential safety dangers, and conducting common safety audits.
Password Administration and Authentication
Relating to sustaining the safety of your Qbittorrent and VPN connections, password administration and authentication play a big position. Weak passwords, default login credentials, and poor authentication strategies can compromise the safety of your connections. To keep away from this, it is essential to make use of sturdy, distinctive passwords for all of your VPN and Qbittorrent accounts. Moreover, allow two-factor authentication (2FA) wherever potential to offer an additional layer of safety. This will embody utilizing authenticator apps, SMS codes, or biometric verification strategies.
- Use a password supervisor to generate and retailer distinctive, sturdy passwords for all of your VPN and Qbittorrent accounts.
- Allow two-factor authentication (2FA) wherever potential to forestall unauthorized entry.
- Usually replace your passwords to keep away from password getting older and potential safety dangers.
Monitoring On-line Actions and Figuring out Potential Safety Dangers
Monitoring your on-line actions and figuring out potential safety dangers is vital to sustaining the safety of your Qbittorrent and VPN connections. You need to use varied instruments to trace on-line actions, together with firewall logs, community exercise screens, and system occasion logs. By monitoring these logs, you possibly can determine potential safety dangers equivalent to suspicious community site visitors, uncommon system exercise, or unauthorized entry makes an attempt.
Firewall logs present a report of incoming and outgoing community site visitors, permitting you to watch and analyze your system’s community exercise.
- Monitor firewall logs and community exercise screens to trace on-line actions and determine potential safety dangers.
- Usually assessment system occasion logs to detect potential safety points and reply promptly.
- Use community intrusion detection methods (NIDS) to detect and stop unauthorized entry makes an attempt.
Safety Audits and Common Software program Updates
Common safety audits and software program updates are important to take care of the safety of your Qbittorrent and VPN connections. A safety audit entails reviewing your system’s safety configuration, figuring out potential vulnerabilities, and implementing essential safety measures. Common software program updates make sure that your system and functions have the most recent safety patches and options.
A safety audit may also help determine potential safety vulnerabilities and guarantee your system is configured to forestall unauthorized entry.
Finest Practices for Safety Audits and Common Software program Updates, Easy methods to bind qbittorrent to vpn
To make sure the safety of your Qbittorrent and VPN connections, comply with these finest practices for safety audits and common software program updates:
- Schedule common safety audits to assessment your system’s safety configuration and determine potential vulnerabilities.
- Apply all safety patches and updates on your working system, functions, and software program.
- Use respected safety software program and hold it up-to-date to forestall malware and different safety threats.
In conclusion, monitoring and sustaining the safety of your Qbittorrent and VPN connections is essential to forestall potential dangers equivalent to knowledge leaks, cyber assaults, and unauthorized entry. By implementing a sturdy safety plan that features monitoring on-line actions, figuring out potential safety dangers, and conducting common safety audits, you possibly can make sure the safety and integrity of your on-line actions.
Superior Methods for Binding Qbittorrent to VPN: How To Bind Qbittorrent To Vpn

Binding Qbittorrent to a VPN utilizing superior strategies entails leveraging extra software program and instruments to make sure a safe and secure connection. By using these strategies, customers can refine their VPN configurations, troubleshoot connectivity points, and keep the integrity of their torrent downloads.
Consumer-Degree Superior Configurations
When configuring Qbittorrent to work with VPN, customers can make use of varied user-level superior configurations to optimize their expertise. One such configuration entails organising a VPN shopper as the first community interface. This may be achieved by creating a brand new community interface, configuring it to make use of the VPN shopper, and assigning it because the default gateway for the system.
- Open Community settings and create a brand new community interface (e.g., VPN Interface).
- Configure the brand new interface to make use of the VPN shopper (e.g., OpenVPN) as the first connection technique.
- Set the VPN Interface because the default gateway for the system.
This configuration ensures that every one community site visitors, together with torrent downloads, passes via the VPN shopper, thus sustaining the anonymity and safety of the person.
VPN Break up-Tunneling with Qbittorrent
One other superior approach entails configuring VPN split-tunneling with Qbittorrent. This enables customers to specify which functions ought to use the VPN connection and which ought to use the common web connection.
- Configure the VPN shopper to allow split-tunneling.
- Specify Qbittorrent as an utility that ought to use the VPN connection.
- Make sure that the split-tunneling configuration is ready up accurately to permit Qbittorrent to speak with the VPN server.
By using VPN split-tunneling, customers can keep the safety and anonymity of their torrent downloads whereas permitting different functions to entry the common web connection.
Further Software program and Instruments for Qbittorrent-VPN Integration
A number of extra software program and instruments can be utilized to reinforce the mixing of Qbittorrent with a VPN. One such instrument is a community supervisor, which may also help customers configure and handle their community interfaces and VPN connections.
- Set up a community supervisor (e.g., Community Supervisor) on the system.
- Configure the community supervisor to handle the VPN connection and Qbittorrent interface.
- Use the community supervisor to troubleshoot and resolve any connectivity points that will come up.
By leveraging these extra software program and instruments, customers can refine their Qbittorrent-VPN configuration, troubleshoot connectivity points, and keep the safety and integrity of their torrent downloads.
Troubleshooting Complicated Connectivity Points
When troubleshooting complicated connectivity points associated to Qbittorrent and VPN, customers ought to begin by checking the VPN connection and Qbittorrent configuration. Make sure that the VPN connection is energetic and secure, and that Qbittorrent is configured to make use of the VPN interface.
- Confirm that the VPN connection is energetic and secure.
- Test the Qbittorrent configuration to make sure it’s utilizing the VPN interface.
- Use diagnostic instruments (e.g., Wireshark) to research community site visitors and determine any points.
By following these steps, customers can troubleshoot complicated connectivity points and keep the safety and integrity of their torrent downloads.
“A safe and secure VPN connection is important for sustaining the anonymity and safety of torrent downloads.”
Abstract
The method of binding qbittorrent to vpn is a vital step in defending on-line identities and sustaining on-line security. It’s a complicated activity that requires persistence, consideration to element, and the willingness to study the intricacies of community communication protocols.
Via this information, customers can grasp the artwork of VPN utilization, troubleshoot frequent connectivity points, and fine-tune their on-line safety measures for the optimum person expertise. Qbittorrent and VPN companies function important instruments for navigating the trendy digital panorama.
Consumer Queries
Can I exploit a free VPN with qbittorrent?
Sure, however bear in mind that free VPNs usually include limitations and tend to gather and promote person knowledge, which may jeopardize your anonymity.
How do I troubleshoot frequent connectivity points between qbittorrent and VPN?
Test your VPN and qbittorrent configurations, ensure you have the right community settings, and modify your qbittorrent settings in accordance with your VPN supplier’s suggestions.
Is it essential to have a high-speed web connection for qbittorrent and VPN?
A dependable web connection is important for seamless efficiency, however a high-speed connection is probably not essential for all duties.
Can I exploit qbittorrent with a number of VPN connections?
Sure, however you will must arrange a number of VPN connections and configure qbittorrent accordingly to make sure easy operation.
How do I configure qbittorrent to make use of a number of VPN connections?
The method entails creating separate VPN connections, organising qbittorrent to make use of every VPN, and adjusting your qbittorrent settings to accommodate a number of VPN connections.