Delving into mapping a community drive, this introduction immerses readers in a singular and compelling narrative, the place the complexities of file sharing are damaged down into tangible, actionable steps. By exploring the ins and outs of community drive mapping, readers will achieve a profound understanding of its significance in enhancing collaboration and productiveness.
In a world the place knowledge is the lifeblood of enterprise, community drive mapping has grow to be an indispensable instrument for seamless communication and knowledge change. By mapping a community drive, customers can entry shared recordsdata and assets straight from their desktop, fostering a way of unity and effectivity within the workspace.
Making ready Your Community Infrastructure
To start out mapping a community drive, it is important to make sure your community infrastructure is ready up appropriately. This consists of the {hardware} and software program elements that allow knowledge switch and storage throughout the community.
Making ready the required infrastructure entails a number of key components, together with routers, switches, and community working techniques. These elements work collectively to facilitate communication between units, guarantee knowledge integrity, and allow environment friendly knowledge switch.
Community routers are liable for connecting a number of networks and directing knowledge between them. They act as a gateway between the native community and the web, enabling units to entry exterior assets and providers.
For community drive mapping, a dependable router is essential. It ensures that knowledge is transmitted precisely and effectively throughout the community, minimizing the chance of information loss or corruption.
This is an instance of a typical community setup:
- Routers: Join units to the web and allow knowledge switch between networks.
- Switches: Join units inside a community and allow knowledge switch between them.
- Community Working System: Supplies a framework for managing community assets and enabling communication between units.
Community working techniques (NOS) present a framework for managing community assets and enabling communication between units. In addition they play a vital function in making certain knowledge integrity and safety throughout the community.
There are a number of NOS choices obtainable, together with:
- Home windows Server
- Linux
- Unix
Every NOS has its personal strengths and weaknesses, and the selection of NOS is dependent upon your particular community necessities and infrastructure.
Listed below are some real-world examples of community setups that help community drive mapping:
- Campus networks: Universities and schools use community drive mapping to allow college students and school to entry shared assets and knowledge throughout the campus.
- Enterprise networks: Massive companies use community drive mapping to allow distant staff to entry firm assets and knowledge from anyplace on this planet.
Selecting a Mapping Technique

In relation to mapping a community drive, there are a number of strategies to select from. Every methodology has its personal benefits and downsides, that are mentioned under. The objective is to pick out probably the most appropriate methodology in your particular wants and infrastructure.
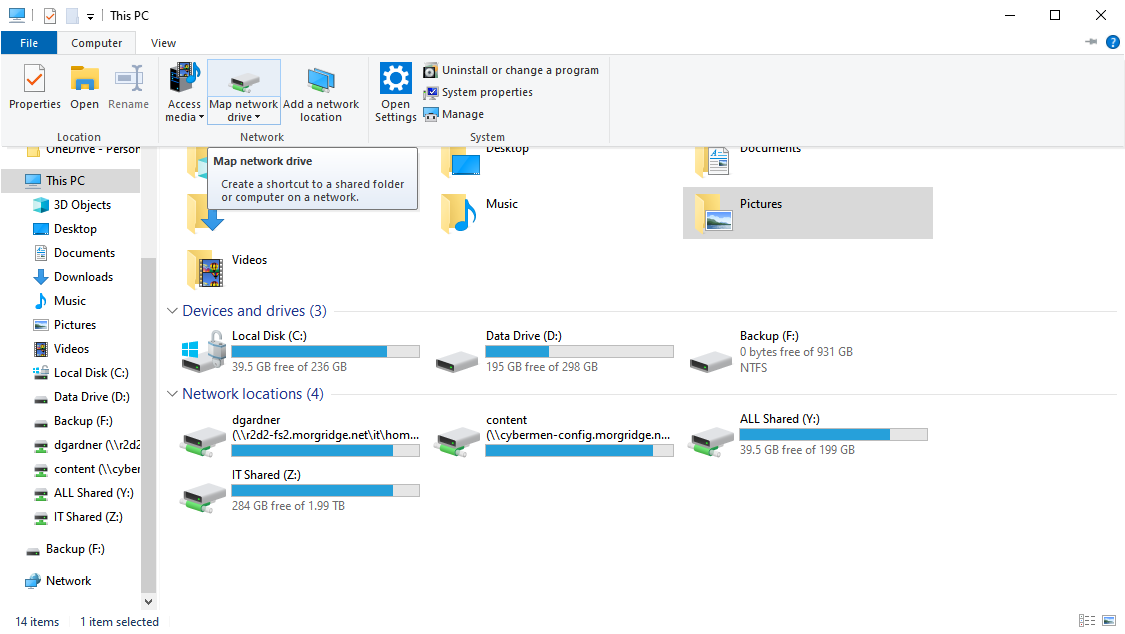
Technique 1: Utilizing the “Map Community Drive” Possibility in Home windows Explorer
This methodology entails utilizing the built-in “Map Community Drive” choice in Home windows Explorer to map a community drive. Listed below are the step-by-step directions:
- Begin by opening Home windows Explorer.
- Navigate to the community location you wish to map by getting into the UNC path or by shopping to the share.
- Proper-click on the community location and choose “Map community drive.”
- Within the “Map Community Drive” window, choose the drive letter you wish to assign to the community location and click on “End.”
The drive will now be mapped to the chosen community location. This methodology is simple and straightforward to make use of, nevertheless it might not be appropriate for bigger organizations or environments the place Group Coverage is in use.
Technique 2: Utilizing Group Coverage
Group Coverage is a characteristic of Home windows that permits directors to centralize and handle settings throughout the community. Utilizing Group Coverage to map community drives is a extra superior methodology that requires administrative privileges and a very good understanding of Group Coverage objects.
This is use Group Coverage to map a community drive:
- Open the Group Coverage Editor (gpedit.msc) and navigate to the “Consumer Configuration” node.
- Below “Administrative Templates,” navigate to the “Community” node and choose “Map Community Drive.”
- Double-click on the “Map Community Drive” coverage and choose “Enabled.”
- Within the “Map Community Drive” window, enter the UNC path of the community location you wish to map.
- Specify the drive letter you wish to assign to the community location.
- Click on “Apply” after which “OK” to save lots of the modifications.
This methodology permits directors to centrally handle community drive mappings throughout the community, making it a extra scalable and manageable choice for bigger organizations.
Desk: Comparability of Mapping Strategies
| Technique | Benefits | Disadvantages |
|---|---|---|
| Technique 1: Utilizing the “Map Community Drive” Possibility in Home windows Explorer | Straightforward to make use of, easy course of, no administrative privileges required | Is probably not appropriate for bigger organizations or environments the place Group Coverage is in use, will be vulnerable to person errors |
| Technique 2: Utilizing Group Coverage | Centralized administration, scalable, manageable, administrative privileges required | Requires administrative privileges and a very good understanding of Group Coverage objects, will be complicated to arrange |
It’s important to guage the professionals and cons of every methodology earlier than deciding which one to make use of in your group. The chosen methodology ought to align together with your infrastructure and meet the wants of your customers.
Superior Community Drive Mapping Methods: How To Mapping A Community Drive

Superior community drive mapping methods allow directors to automate and streamline community drive mapping processes, lowering administrative overhead and bettering person productiveness. These methods can be utilized to create dynamic community drive mappings, implement drive mapping insurance policies, and combine community drive mapping with group insurance policies.
Utilizing PowerShell Scripts
For instance, you should use PowerShell to map a drive to a community location robotically, or to implement drive mapping insurance policies throughout a company. To map a drive utilizing PowerShell, you should use the New-PSDrive cmdlet, as proven within the following instance:
“`
New-PSDrive -Title Z -PSProvider FileSystem -Root servershare
“`
This command maps the drive letter Z to the community location servershare.
Utilizing Group Coverage Preferences
Group Coverage preferences are one other superior community drive mapping approach that permits directors to create dynamic community drive mappings, implement drive mapping insurance policies, and combine community drive mapping with group insurance policies. Group Coverage preferences can be utilized to map drives to particular community places based mostly on person or pc properties.
Evaluating and Contrasting Advantages and Drawbacks
When utilizing superior community drive mapping methods, there are a number of advantages to think about, together with:
“`
- Improved automation: Superior community drive mapping methods can automate community drive mapping processes, lowering administrative overhead and bettering person productiveness.
- Elevated safety: Superior community drive mapping methods can implement drive mapping insurance policies, stopping unauthorized drive mappings and bettering safety.
- Dynamic mappings: Superior community drive mapping methods can create dynamic community drive mappings, permitting customers to entry community places with out requiring guide drive mapping.
- Group coverage integration: Superior community drive mapping methods can combine community drive mapping with group insurance policies, permitting directors to implement drive mapping insurance policies throughout a company.
“`
Dangers and Limitations
Nonetheless, there are additionally potential dangers and limitations to think about when utilizing superior community drive mapping methods:
“`
- Script complexity: Superior community drive mapping methods can require complicated scripting, which will be difficult for directors with restricted scripting expertise.
- Safety dangers: Superior community drive mapping methods can introduce safety dangers if not correctly configured, permitting unauthorized drive mappings or entry to delicate community places.
- Infrastructure necessities: Superior community drive mapping methods can require further infrastructure, akin to PowerShell or Group Coverage infrastructure, which might add complexity and value.
- Interoperability points: Superior community drive mapping methods can introduce interoperability points, significantly if utilizing a number of instruments or applied sciences.
“`
Finest Practices for Community Drive Mapping
Establishing greatest practices for community drive mapping is crucial to make sure seamless collaboration and knowledge safety. A well-structured community drive mapping technique helps to streamline entry to shared assets, scale back errors, and mitigate potential safety dangers. This chapter will focus on the perfect practices for community drive mapping, together with creating clear folder buildings and utilizing permissions successfully.
Creating Clear Folder Buildings
A transparent folder construction is essential for environment friendly navigation and knowledge group. To create an efficient folder construction, think about the next ideas:
- Categorize folders based mostly on performance (e.g., by division, undertaking, or exercise) somewhat than location or system.
- Use descriptive and concise folder names to keep away from confusion.
- Create a standardized naming conference for folders and subfolders.
- Arrange folders and subfolders in a hierarchical construction, utilizing folders to group associated assets.
- Set up clear tips for folder permissions and entry management.
Clear folder buildings scale back info overload, reduce confusion, and promote quick access to shared assets.
For instance, think about an organization with a number of departments that require shared entry to tasks and assets. A transparent folder construction may very well be organized as follows:
- Firm
- Finance
- Gross sales Reviews
- Monetary Statements
- Human Sources
- Worker Information
- Advantages Packages
- Advertising and marketing
- Marketing campaign Supplies
- Advertising and marketing Analytics
By implementing this construction, customers can simply entry particular assets associated to their departments with out being overwhelmed by a cluttered folder hierarchy.
Utilizing Permissions Successfully
Correct permission administration is crucial to keep up knowledge safety and forestall unauthorized entry. Contemplate the next greatest practices for permissions:
- Set up clear roles and duties inside the group to outline entry necessities.
- Use permissions to manage entry to particular folders, assets, or recordsdata.
- Designate house owners and directors for folders and assets to handle entry and permissions.
- Use teams or roles to simplify permission administration and scale back administrative burden.
For instance, think about a advertising staff that requires entry to marketing campaign supplies however not monetary statements. The advertising staff chief will be designated the proprietor of the Advertising and marketing folder, with the power to grant entry to particular staff members and exterior collaborators whereas limiting entry to HR and monetary assets.
By implementing efficient permission administration, organizations can be sure that knowledge stays safe and solely approved customers have entry to delicate assets.
Advantages of Finest Practices for Community Drive Mapping, Tips on how to mapping a community drive
By implementing these greatest practices for community drive mapping, organizations can expertise improved collaboration, enhanced knowledge safety, and elevated effectivity. Efficient folder buildings and permissions administration allow customers to simply entry assets, scale back errors, and mitigate potential safety dangers. This results in elevated productiveness, lowered IT prices, and improved enterprise continuity.
Conclusion
As we have navigated the panorama of community drive mapping, it is grow to be evident that this course of just isn’t merely a technical train, however a strategic instrument for enhancing productiveness and collaboration. By embracing the ideas of community drive mapping, customers can unlock new avenues for innovation, creativity, and development, thereby revolutionizing the best way groups work collectively.
FAQ Nook
Q: What are the first {hardware} necessities for mapping a community drive?
A: The first {hardware} necessities for mapping a community drive embrace a functioning community router, a linked system with a suitable working system, and adequate RAM to deal with the mapped drive.
Q: Can I map a community drive on a Mac?
A: Sure, you possibly can map a community drive on a Mac utilizing the ‘Connect with Server’ characteristic within the Finder software or through the use of the ‘Map Community Drive’ choice within the Disk Utility instrument.
Q: How do I troubleshoot frequent points associated to community drive mapping?
A: To troubleshoot frequent points associated to community drive mapping, customers can begin by verifying their community connection, checking for any firewall or antivirus software program conflicts, and making certain that the mapped drive is appropriately configured.