Methods to reclaim area from disk shadows copies, you may be questioning why you are working low on disk area regardless of having ample bodily storage. The reality is that disk shadows copies, created by Home windows for information safety, typically devour a major quantity of area in your arduous drive.
On this article, we’ll delve into the world of disk shadow copies, exploring their objective, figuring out widespread places and file extensions, and offering step-by-step guides to manually deleting or archiving them, limiting their progress, redirecting them to different disks or storage gadgets, and far more.
Understanding Disk Area Shadow Copies and Their Function in Knowledge Storage

Disk area shadow copies are primarily backups of your pc’s arduous drive, saved on a separate arduous drive or exterior storage gadget. This idea is also referred to as Quantity Shadow Copy Service (VSS) or System Safety in Home windows. It was designed to assist customers get well information in case of a system crash, malware assault, or different information loss conditions.
These backup copies are created at common intervals, both manually or mechanically, and retailer earlier variations of your recordsdata and folders. The primary concept behind shadow copies is to forestall information loss by permitting customers to revert again to earlier variations of their recordsdata if one thing goes improper.
Advantages of Utilizing Shadow Copies
Utilizing shadow copies affords a number of advantages for information safety, together with:
- Model management: You’ll be able to simply entry and restore earlier variations of your recordsdata when you’ve made modifications and wish to return to an earlier model.
- Backup and restoration: Shadow copies function a backup of your information, permitting you to get well your recordsdata in case of a system crash or different information loss occasions.
- Malware safety: Shadow copies can assist you get well your recordsdata in case your system has been contaminated with malware or a virus.
- File administration: Shadow copies allow you to roll again modifications made to your recordsdata and folders, which will be significantly helpful for system directors and customers who work with delicate information.
Drawbacks of Utilizing Shadow Copies
Whereas shadow copies provide a number of advantages, there are additionally some drawbacks to think about:
- Area necessities: Shadow copies require further disk area to retailer the backup copies, which may result in low disk area points if not managed correctly.
- Useful resource consumption: Creating and sustaining shadow copies can devour system assets, probably slowing down your pc.
- Complexity: Managing shadow copies will be complicated, particularly for customers with restricted technical information.
- Restricted model retention: Shadow copies typically have a restricted retention interval, which means that older variations of your recordsdata are deleted periodically to release disk area.
Understanding Disk Area Necessities
On the subject of managing disk area for shadow copies, there are some things to bear in mind:
- Dimension of shadow copies: The scale of shadow copies is dependent upon the quantity of information being backed up, in addition to the variety of variations retained.
- Retention interval: The longer the retention interval, the extra disk area will likely be required to retailer the backup copies.
- Disk area allocation: You’ll be able to allocate a certain quantity of disk area for shadow copies, which will likely be used for storing the backup copies.
Disabling or Configuring Shadow Copies
If you wish to disable or configure shadow copies, observe these steps:
- Open System Safety in Home windows by trying to find it within the Begin menu.
- Click on on “Flip off System Safety” to disable shadow copies for the chosen drive.
- Click on on “Configure” to regulate the shadow copy settings, such because the retention interval and disk area allocation.
- Click on “OK” to save lots of the modifications.
By understanding the advantages and disadvantages of shadow copies, you can also make knowledgeable selections about learn how to handle disk area and defend your information.
Implementing System Settings to Restrict Shadow Copy Development
Shadow copies, also referred to as Quantity Snapshot Service (VSS) snapshots, are a vital function in Home windows for backing up recordsdata and system state. Nevertheless, they will rapidly devour disk area, particularly if not correctly managed. To stop this, understanding learn how to management the frequency and length of shadow copy creation is essential.
While you arrange your system settings to restrict shadow copy progress, you might be primarily regulating how typically and for a way lengthy shadow copies are retained in your disk. This may be finished by configuring the next choices:
Setting a Most Variety of Shadow Copies
To regulate shadow copy progress by limiting the variety of snapshot copies, you possibly can set a most quantity to retain. This may be finished by way of the Home windows built-in Disk Administration instrument. Open Disk Administration, right-click on the quantity you wish to configure, and choose Properties. Within the Shadow Copies tab, you possibly can regulate the Most dimension (% quantity) slider to restrict the area utilized by shadow copies or set a most variety of snapshots.
Setting a most dimension for shadow copies means that you can management the quantity of disk area consumed by these snapshots. For instance, when you have a 256 GB drive and also you set the utmost dimension for shadow copies to 10% of the whole quantity, it could be 26 GB. Because of this shadow copies would solely devour 26 GB of disk area.
Setting a Most Age for Shadow Copies
To regulate shadow copy progress by limiting the length of shadow copies, you possibly can set a most retention interval. This may also be finished by way of Disk Administration or the built-in Shadow Copies tab. By setting a most age for shadow copies, you possibly can be certain that older snapshots are mechanically deleted after a sure interval.
The utmost age setting means that you can decide how lengthy shadow copies are retained on the disk. As an example, when you set the utmost age for shadow copies to 14 days, it implies that snapshots older than 14 days will likely be mechanically deleted from the disk.
Setting a Most Frequency for Shadow Copy Creation
To regulate shadow copy progress by regulating how typically shadow copies are created, you possibly can set a most frequency. This may be finished by way of the Home windows built-in Activity Scheduler instrument or the VSSAdmin.exe command-line instrument. By setting a most frequency for shadow copy creation, you possibly can stop snapshots from being created too ceaselessly, which may result in extreme disk area utilization.
The utmost frequency setting means that you can management how typically shadow copies are created. For instance, when you set the utmost frequency for shadow copy creation to each 8 hours, it implies that snapshots will solely be created each 8 hours, stopping them from consuming an excessive amount of disk area.
Affect of Altering Default Settings on Disk Storage Utilization
Altering the default settings for shadow copy progress has a major impression on disk storage utilization. By limiting the variety of snapshots, the utmost dimension, most age, or most frequency, it can save you disk area and stop extreme utilization.
The impression of adjusting default settings on disk storage utilization will be illustrated as follows: Suppose you have got a 256 GB drive with 100% utilization. For those who set the utmost dimension for shadow copies to 10% (26 GB), it can save you 74 GB of disk area. Equally, when you set the utmost age to 14 days, you possibly can stop 14-day-old snapshots from consuming disk area, liberating up round 2.3 GB of disk area (assuming 200 MB per snapshot).
Keep in mind that the precise impression will rely in your particular system configuration and utilization patterns.
Using Various Disks or Storage Gadgets for Shadow Copies
Redirecting shadow copy storage to a separate quantity or disk array could be a viable resolution for managing disk area. This technique means that you can release area in your main disk and offload the burden of storing system picture recordsdata to a secondary storage gadget.
This different method will be significantly useful for programs with restricted disk area or people who require frequent system picture backups. By using a separate disk or storage array for shadow copies, you possibly can preserve a clear and clutter-free main disk whereas nonetheless making certain entry to system restoration factors.
Redirecting Shadow Copy Storage
To redirect shadow copy storage, observe these steps:
- Determine the quantity the place you wish to retailer shadow copies. This could be a separate disk, a storage array, or a community location.
- Open the Home windows Disk Administration Console (Press Win+R and kind diskmgmt.msc to open it).
- Proper-click on the quantity you wish to use for shadow copies and choose Properties.
- Go to the Shadow Copies of Chosen Drives tab and verify the field subsequent to the quantity you created.
Notice that the particular steps could differ relying in your model of Home windows.
Benefits and Challenges
Using a separate disk or storage array for shadow copies affords a number of advantages, together with:
- Elevated disk area: By shifting shadow copies to a separate storage gadget, you possibly can release area in your main disk.
- Improved system efficiency: With shadow copies saved on a separate disk, your system will expertise improved efficiency and responsiveness.
- Enhanced catastrophe restoration: Having system picture recordsdata saved on a separate gadget makes it simpler to get well your system in case of a catastrophe or {hardware} failure.
Nevertheless, there are additionally some challenges related to utilizing a secondary storage gadget for shadow copies:
- Extra value: You could incur further prices for buying a separate storage gadget or increasing your present storage array.
- Complexity: Configuring and managing shadow copies on a separate storage gadget can add complexity to your system configuration.
- Knowledge switch: You have to to switch system picture recordsdata to the separate storage gadget, which can require further effort and time.
Make sure that your secondary storage gadget is correctly configured and that you’ve got a transparent understanding of learn how to handle shadow copies on the brand new gadget.
Finest Practices for Shadow Copy Administration in Shared Environments
In shared environments, managing shadow copies successfully is essential to make sure optimum information storage and stop conflicts between a number of customers or workloads. This includes coordinating shadow copy administration, speaking methods to stakeholders, and implementing finest practices to keep up a balanced and environment friendly storage system.
In a shared surroundings, it is important to determine a unified shadow copy administration technique to keep away from conflicts and inconsistencies. This consists of defining roles and obligations, setting clear insurance policies, and usually monitoring and adjusting the shadow copy administration course of.
Coordinating Shadow Copy Administration Throughout A number of Customers or Workloads, Methods to reclaim area from disk shadows copies
When managing shadow copies in a shared surroundings, contemplate the next finest practices to make sure seamless coordination:
- Designate a shadow copy administrator: Appoint a single particular person to supervise all the shadow copy administration course of, making certain consistency and effectivity throughout the system.
- Set up clear insurance policies and procedures: Develop and talk clear tips for shadow copy administration, together with information retention, backup and restore processes, and battle decision.
- Repeatedly monitor and regulate: Schedule common checks to make sure the shadow copy administration course of is working easily, regulate settings as wanted, and handle any points promptly.
- Implement computerized shadow copy scheduling: Automate shadow copy creation and deletion to forestall handbook errors and inconsistencies.
- Monitor storage capability: Repeatedly observe storage utilization to forestall overconsumption and guarantee ample area for shadow copies.
- Foster collaboration and communication: Encourage open communication amongst stakeholders to forestall conflicts, share information, and handle issues.
Speaking Shadow Copy Methods to Stakeholders
Efficient communication is significant to make sure stakeholders perceive the shadow copy administration technique, roles, and obligations.
- Develop a communication plan: Artikel the channels, frequency, and content material of communication to maintain stakeholders knowledgeable and engaged.
- Craft clear and concise messaging: Use easy language to clarify complicated shadow copy administration ideas, avoiding technical jargon and emphasizing key takeaways.
- Present common updates and suggestions: Schedule common conferences or ship common updates to maintain stakeholders knowledgeable about shadow copy administration progress and handle issues.
- Set up a suggestions loop: Encourage stakeholders to share issues, concepts, or ideas, and reply promptly to keep up transparency and belief.
Educating Stakeholders on Shadow Copy Finest Practices
To make sure stakeholders are outfitted to handle shadow copies successfully, present training and coaching on really helpful finest practices.
- Supply common coaching periods: Schedule workshops or on-line periods to show stakeholders about shadow copy administration, information retention, and backup and restore processes.
- Present documentation and assets: Supply entry to clear, concise documentation, FAQs, and on-line assets to complement coaching and help.
- Encourage information sharing: Facilitate alternatives for stakeholders to share their information and experiences, selling a tradition of collaboration and experience.
Guaranteeing Shadow Copy Compliance and Knowledge Safety
To take care of compliance and safety, implement strict information entry controls, encrypt delicate information, and cling to regulatory necessities.
| Finest Follow | Rationalization |
|---|---|
| Implement information entry controls | Restrict entry to delicate information to approved personnel, utilizing role-based entry controls and strict authentication. |
| Encrypt delicate information | Defend delicate information utilizing encryption, each at relaxation and in transit, to forestall unauthorized entry and information breaches. |
| Adhere to regulatory necessities | Adjust to related rules, comparable to GDPR, HIPAA, or PCI-DSS, to make sure information safety and defend client info. |
By implementing these finest practices for shadow copy administration in shared environments, you possibly can preserve a balanced and environment friendly storage system, guarantee consistency and cooperation amongst stakeholders, and safeguard your group’s information safety and compliance.
Figuring out and Addressing Shadow Copy-Associated Efficiency Points: How To Reclaim Area From Disk Shadows Copies
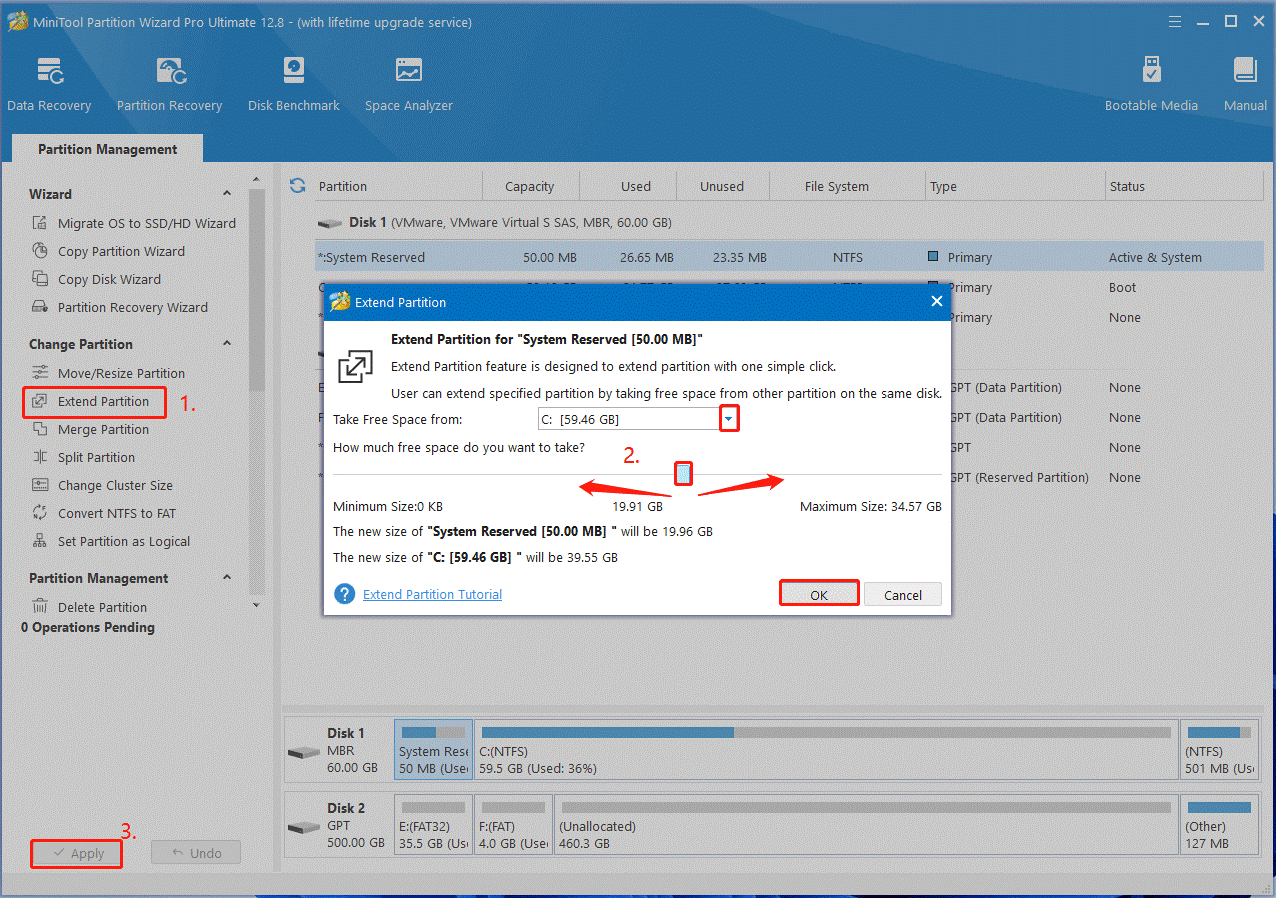
![How to Delete Shadow Copies on Windows 11/10/Server? [4 Ways] - MiniTool How to Delete Shadow Copies on Windows 11/10/Server? [4 Ways] - MiniTool](https://www.minitool.com/images/uploads/articles/2023/02/how-to-delete-shadow-copies/how-to-delete-shadow-copies-7.png)
Shadow copy operations can generally impression system efficiency, inflicting bottlenecks and slowing down your disk utilization. To deal with these points, it is important to know the components contributing to shadow copy-related efficiency issues and learn how to troubleshoot them.
The disk configuration and storage expertise used can considerably have an effect on shadow copy efficiency. Understanding how completely different configurations impression shadow copy operations is essential for optimizing system efficiency.
Monitoring System Sources
Monitoring system assets comparable to CPU, reminiscence, and disk utilization is significant for figuring out efficiency bottlenecks associated to shadow copy operations. This may be finished utilizing built-in Home windows instruments like Activity Supervisor or Efficiency Monitor.
- Activity Supervisor: This instrument supplies a real-time view of system useful resource utilization, together with CPU, reminiscence, disk, and community utilization.
- Efficiency Monitor: This instrument means that you can monitor system useful resource utilization and efficiency counters, serving to you establish efficiency bottlenecks.
Analyzing Efficiency Logs
Analyzing efficiency logs can present priceless insights into system efficiency points associated to shadow copy operations. Efficiency logs comprise particulars about system exercise, together with useful resource utilization and occasion information.
- Efficiency logs will be seen utilizing the built-in Reliability Monitor instrument in Home windows.
- Analyzing efficiency logs can assist establish patterns and tendencies in system efficiency, permitting you to make knowledgeable selections about optimizing system efficiency.
Configuring Shadow Copy Settings
Configuring shadow copy settings can assist optimize system efficiency by limiting the variety of shadow copies created and saved on the disk. This may be finished by adjusting the Max Dimension, Retention Interval, and different settings.
- Adjusting the Max Dimension setting can assist restrict the quantity of disk area utilized by shadow copies.
- Configuring the Retention Interval can assist be certain that shadow copies aren’t saved indefinitely.
Utilizing Third-Social gathering Instruments
Utilizing third-party instruments can assist optimize system efficiency by offering superior options and settings for managing shadow copy operations. These instruments can assist establish efficiency bottlenecks and supply suggestions for enhancing system efficiency.
- Third-party instruments can present superior options for monitoring system assets and analyzing efficiency logs.
- Some third-party instruments provide customizable settings for configuring shadow copy operations.
Creating Scripts or Instruments to Automate Shadow Copy Administration Duties
As your system grows and your customers’ wants turn into extra complicated, handbook administration of shadow copies can turn into a frightening process. Automating these duties utilizing customized scripts or instruments can prevent time, scale back errors, and enhance total effectivity. On this part, we’ll discover the world of scripting languages and instruments appropriate for automating shadow copy administration.
Scripting Languages and Instruments Appropriate for Shadow Copy Administration
Shadow copy administration will be streamlined utilizing numerous scripting languages and instruments. PowerShell, a preferred alternative for Home windows directors, affords a strong set of cmdlets for managing shadow copies. Different scripting languages, like Python and Perl, may also be used to automate duties associated to shadow copy administration.
When selecting a scripting language or instrument, contemplate the next components:
– Ease of use: Choose a language or instrument that you simply’re conversant in or one which has a delicate studying curve.
– Integration: Make sure the chosen scripting language or instrument integrates seamlessly along with your present infrastructure and software program.
– Complexity: Take into account the extent of complexity your shadow copy administration duties require and select a language or instrument that may deal with them effectively.
Scripting Languages for Shadow Copy Administration:
- PowerShell: A well-liked alternative for Home windows directors, PowerShell affords a variety of cmdlets for managing shadow copies.
- Python: A flexible and widely-used scripting language, Python can be utilized to automate duties associated to shadow copy administration.
- Perl: A mature and dependable scripting language, Perl can be utilized to handle shadow copies and different system duties.
Instruments for Shadow Copy Administration:
- Shadow Copy Administration Instrument: A free, open-source instrument that simplifies shadow copy administration duties.
- Shadow Copies Supervisor: A business instrument that gives superior options for managing shadow copies.
Designing and Implementing a Customized Script or Instrument for Shadow Copy Administration
When designing and implementing a customized script or instrument for shadow copy administration, contemplate the next finest practices:
– Outline clear targets: Decide the particular duties you wish to automate and create a transparent set of aims.
– Assess system assets: Consider system assets and make sure the script or instrument will not impression efficiency.
– Implement error dealing with: Develop a strong error-handling mechanism to forestall script or instrument failures.
– Check totally: Rigorously check the script or instrument to make sure it really works as supposed.
Scripting Concerns:
| Scripting Language | Instance Instructions | Description |
|---|---|---|
| PowerShell |
|
PowerShell supplies a variety of cmdlets for managing shadow copies. |
| Python |
|
Python can be utilized to execute PowerShell cmdlets and automate duties. |
Finest Practices:
“At all times check your script or instrument in a non-production surroundings earlier than implementing it in manufacturing.”
By following these finest practices and choosing the proper scripting language or instrument, you possibly can effectively automate shadow copy administration duties and scale back errors, enhancing total system efficiency and reliability.
Epilogue
Reclaiming area from disk shadows copies is just not an advanced process, but it surely requires you to know their function in information storage and be prepared to manually or mechanically handle them to release disk area. By implementing the methods Artikeld on this article, you’ll optimize your system’s efficiency, scale back storage utilization, and stop potential bottlenecks.
High FAQs
Q: Can I disable shadow copies to release disk area?
A: Sure, you possibly can disable shadow copies, however bear in mind that this may impression your system’s skill to get well information in case of a failure.
Q: How typically do shadow copies expire?
A: Shadow copies normally expire after three months, however this length will be adjusted primarily based in your system’s configuration.
Q: Can I redirect shadow copies to an exterior arduous drive?
A: Sure, you possibly can redirect shadow copies to an exterior arduous drive, however be certain that the exterior drive has ample area and is correctly linked to your system.
Q: What are the dangers of deleting shadow copies?
A: Deleting shadow copies can result in information loss if a system failure happens and you should get well information from these copies.