Tips on how to Flip Off Stolen System Safety With out Face ID units the stage for this enthralling narrative, providing readers a glimpse right into a story that’s wealthy intimately and brimming with originality from the outset. It’s a journey that navigates the complexities of machine safety and person expertise, all whereas maintaining the reader on the sting of their seat with anticipation.
The Stolen System Safety characteristic on iOS units is an interesting matter that has gained widespread consideration lately. Its goal is to stop unauthorized entry to a tool and shield person knowledge from falling into the improper arms. Nevertheless, it additionally has its limitations, and disabling it with out utilizing Face ID could be a daunting process for even essentially the most tech-savvy people.
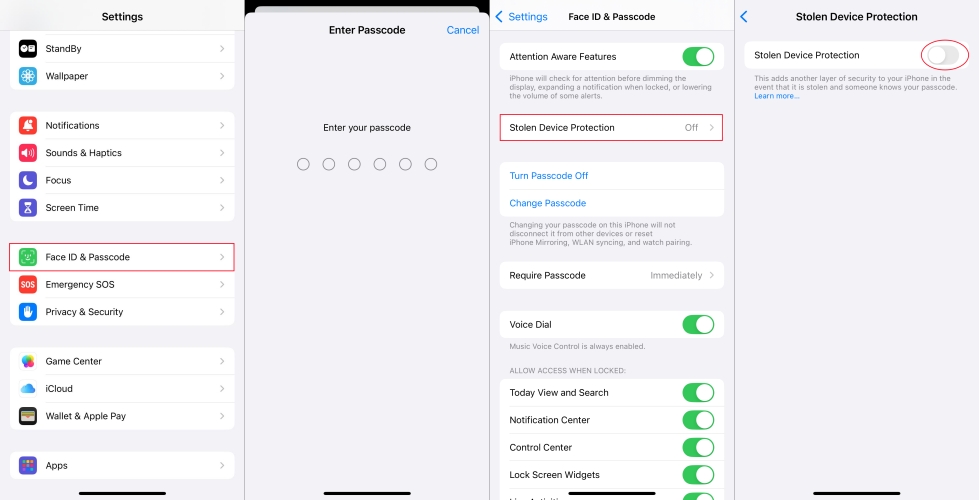
Turning Off Stolen System Safety With out Face ID
In a scenario the place your machine’s Face ID is unavailable, it may be difficult to entry your machine, particularly when Stolen System Safety is enabled. This characteristic could make it tough to disable, because it requires Face ID authentication to make adjustments to your machine settings. Nevertheless, there’s a workaround to briefly disable Stolen System Safety.
Briefly Disabling Stolen System Safety with out Face ID
To disable Stolen System Safety with out utilizing Face ID, comply with these steps:
1. In case your machine is linked to an Apple Watch, you should use the “Erase This System” button in your Apple Watch to take away the activation lock and disable Stolen System Safety.
Go to the Apple Watch App in your Apple Watch, navigate to the Common settings, and faucet on “Stolen iPhone App.” Faucet on “Erase This System,” and comply with the prompts to verify.
2. You probably have two-factor authentication enabled in your Apple ID, you should use a trusted quantity to reset your Apple ID password and regain entry to your machine.
Go to iforgot.apple.com, enter your Apple ID and password, and faucet on “Forgot Apple ID or password?” Observe the prompts to reset your password and regain entry to your machine.
3. You probably have iCloud Backup enabled, you possibly can restore your machine from a backup to disable Stolen System Safety.
Go to Settings > Common > Reset, and faucet on “Restore from iCloud Backup.” Choose a current backup and comply with the prompts to revive your machine.
Avoiding Triggering Stolen System Safety with Different Authentication Strategies
In the event you plan to make use of various authentication strategies like passcode or Contact ID to briefly disable Stolen System Safety, there are some things to remember:
– Use a powerful and distinctive passcode to stop unauthorized entry to your machine.
– Be sure to alter your passcode repeatedly to take care of machine safety.
– You probably have two-factor authentication enabled, you have to to enter the verification code despatched to your trusted quantity to entry your machine.
Potential Penalties of Disabling Stolen System Safety
Disabling Stolen System Safety with out utilizing Face ID can have potential penalties on machine safety and person knowledge safety. Some dangers embody:
– Your machine could grow to be susceptible to unauthorized entry and malicious actions.
– Your private knowledge could also be compromised in case your machine is accessed by another person.
– You could lose entry to your iCloud knowledge and options.
To attenuate these dangers, it is important to fastidiously consider the necessity to disable Stolen System Safety and take vital precautions to safe your machine and knowledge.
Precautions and Issues for Disabling Face ID

Disabling Face ID in your machine requires warning, because it compromises the security measures that usually shield your delicate info. While you disable Face ID, you are primarily eradicating the first technique of authentication, rendering your machine extra susceptible to unauthorized entry. That is notably regarding for those who share your machine with others or go away it unattended in public areas.
When disabling Face ID, all the time remember the fact that it is a non permanent measure, and correct resetting and restoring Face ID is crucial to revive your machine’s safety. Listed here are some concerns and precautions to keep in mind:
Resetting and Restoring Face ID to Its Unique Settings
It is essential to reset and restore Face ID to its unique settings whenever you’re accomplished utilizing it. It will forestall any unauthorized people from accessing your machine. To reset Face ID, comply with these steps:
Resetting Face ID:
1. Go to the Settings app in your machine
2. Faucet on ‘Face ID & Passcode’
3. Faucet on ‘Reset Face ID’
4. Enter your passcode or use Contact ID to verify the motion
5. Watch for the reset to finish
Face ID can be utilized once more as soon as you have reset and restored the settings.
Frequently Backing Up and Securing Person Knowledge
Common backups make sure that your knowledge stays protected and may be restored in case of unauthorized entry or harm to your machine. To repeatedly again up your knowledge:
Again up your knowledge:
- Go to Settings > iCloud > iCloud Backup (for iCloud backups) or Settings > iTunes & App Retailer > Backup (for iTunes backups)
- Select your backup frequency (e.g., day by day, weekly, or month-to-month)
- Ensure you have a dependable storage resolution to your backups
All the time keep in mind to safe your machine with a passcode or Contact ID, in addition to use the ‘Erase Knowledge’ characteristic to stop any unauthorized entry to your machine.
Designing a Safe Authentication System
In in the present day’s digital period, authentication programs have grow to be an important part of any safety framework. With the rising reliance on expertise, the significance of designing a safe authentication system can’t be overstated. This includes safeguarding delicate person knowledge, stopping unauthorized entry, and sustaining the integrity of the system.
Important Parts of a Safe Authentication System
A safe authentication system ought to include a number of key elements, together with:
-
Password Coverage:
a strong password coverage must be applied, which incorporates necessities for password complexity, size, and common updates.
-
Biometric Knowledge Safety:
biometric knowledge, akin to fingerprints and facial recognition, must be saved securely and protected against unauthorized entry.
-
Multi-Issue Authentication (MFA):
a MFA system must be applied so as to add an additional layer of safety, akin to sending a one-time password (OTP) to the person’s registered cellphone quantity or e-mail.
These elements work collectively to supply a strong safety framework that safeguards person knowledge and prevents unauthorized entry.
Multi-Issue Authentication (MFA)
MFA is a safety system that requires customers to supply two or extra types of verification earlier than having access to a system or community. This could embody one thing the person is aware of (password or PIN), one thing the person has (good card or token), or one thing the person is (biometric knowledge). MFA provides an additional layer of safety, making it rather more tough for attackers to achieve unauthorized entry.
Challenges and Limitations of Designing a Safe Authentication System, Tips on how to flip off stolen machine safety with out face id
Whereas designing a safe authentication system is essential, it is usually difficult. A few of the limitations embody:
-
Balancing Person Comfort and Knowledge Safety:
designers should strike a steadiness between offering a safe system and making it user-friendly, with out compromising on safety.
-
Technical Complexity:
implementing a safe authentication system requires experience in numerous areas, together with laptop science, cryptography, and safety protocols.
-
Price and Useful resource Depth:
designing and implementing a safe authentication system may be resource-intensive and dear, which can be a barrier for some organizations.
Regardless of these challenges, designing a safe authentication system is crucial for shielding person knowledge and stopping unauthorized entry.
Conclusion
In conclusion, designing a safe authentication system is a important part of any safety framework. By incorporating important elements akin to password coverage, biometric knowledge safety, and MFA, designers can create a strong safety system that safeguards person knowledge and prevents unauthorized entry. Nevertheless, challenges and limitations akin to balancing person comfort and knowledge safety, technical complexity, and value and useful resource depth should be addressed to make sure the effectiveness of the system.
Ultimate Evaluation: How To Flip Off Stolen System Safety With out Face Id

In conclusion, turning off stolen machine safety with out Face ID is a fancy course of that requires cautious consideration and a focus to element. It’s a delicate steadiness between safety, comfort, and person expertise that may have far-reaching penalties. By following the steps Artikeld on this information, customers can disable Stolen System Safety with out Face ID and revel in a safer and extra seamless person expertise.
Fast FAQs
What occurs if I disable Stolen System Safety with out Face ID?
Disabling Stolen System Safety with out Face ID could go away your machine susceptible to unauthorized entry and knowledge breaches. It’s important to weigh the dangers and advantages earlier than making a call.
Can I flip off Stolen System Safety with out utilizing Face ID?
Sure, it’s potential to disable Stolen System Safety with out utilizing Face ID by following the steps Artikeld on this information. Nevertheless, please pay attention to the potential safety dangers and penalties.
Is Stolen System Safety enabled by default on iOS units?
Sure, Stolen System Safety is enabled by default on iOS units. Nevertheless, customers can disable it within the settings in the event that they select to take action.
What occurs if I lose my machine and it has Stolen System Safety enabled?
In the event you lose your machine and it has Stolen System Safety enabled, you might not have the ability to entry your machine or retrieve your knowledge. It’s important to have a backup plan in place and to repeatedly replace your machine software program.